If you haven’t read about heartbleed bug, it’s pretty serious one you should know about. In a nutshell it exploits OpenSSL vulnerability to read system memory of computers/machines/applicances protedted by affected versions of OpenSSL. This means a hacker can steal your encryption keys as well as see unencrypted form of traffic that was encrypted. Talk about passwords, credit cards, any information you deemed secure and trusted only to an SSL connection!
You can read whole lot of gory details here: http://heartbleed.com/
If you are users of KEMP LoadMaster, you should immediately patch your systems to protect yourselves from this known and pretty serious vulnerability. Here’s how you can check if you are affected. Go to http://possible.lv/tools/hb. Type in the URL protected by SSL and is served by virtual service configured on your LoadMaster. If you running any of the affected versions, you will be shown a message akin to the one below:
To obtain patch for your affected version, head over to KEMP Forums. You will find details to download the patch over there.
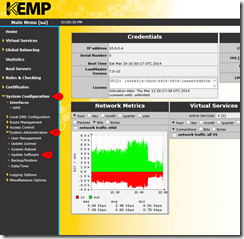
Applying the patch is simple operation too… launch LoadMaster Web UI and go to System Configuration –> System Administration –> Update Software
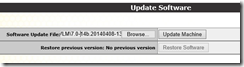
On Update Software page, select appropriate patch file and click “Update Machine”
Understand that this operation has impact on your production environment. You will need to reboot KEMP LoadMaster after applying this patch. Follow the instructions and reboot when asked.
When your LoadMaster reboots, you should be able to perform heartbleed test we performed above and it should look something like this instead:
Cheerios!